This utility is designed specially for network administrators and computer security professionals, who need correct and fast retrieval of all country information for an IP-address or a hostname, allocated IP-address It blocks and other network data details. At present, when hundreds of domains resembling each other appear everyday, Arm Whois becomes a real must-have tool not only for network and PC security professionals but also for ordinary users.
Arm Whois helps to obtain the answers to such questions as: who the owner of the domain is and when the domain was registered. In addition, it shows the owner’s contact information. As Arm Whois is able to view an allocated IP-address block, it also provides the information on the owner of the IP address block and the host location. This utility finds out the administrator and technical support contact information. Unlike standard Whois utilities, Arm Whois can find detailed information about a computer located in any part of the world by automatically performing intelligent search of the right database and then make a query within it. It enables a user to look up all available information about an IP address, hostname or domain, including details concerning country, state, city and the name of the network provider.
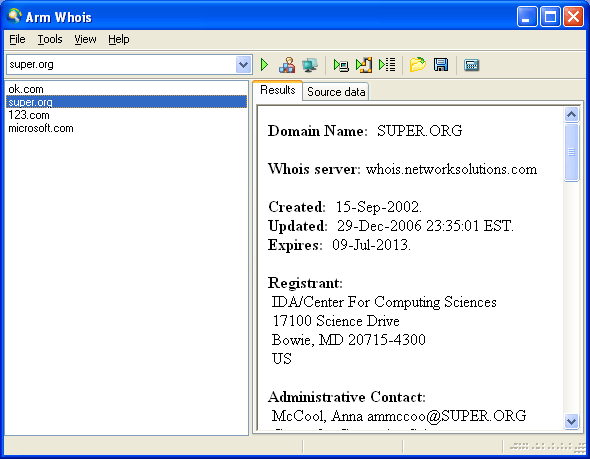
The program has an extremely convenient interface, which lets a user start searching right from the main window without the need for a user manual. A user only has to type the name of the domain into a search line and specify the necessary settings. Thus, Arm Whois offers to choose the query type: by IP-address, domain, or choice. Or, there is an option adding or removing comments. Querying starts with a click on the ‘Go’ button. Then, the results of the request will be displayed in a large field below in a readable and accurate form. What is important, Arm Whois delivers all the related records within a few seconds. Arm Whois can save the obtained information to a text file, process lists of IP addresses or domains.
Arm Whois 2.0 helps you find answers to important questions such as:
* Who is the owner of the domain?
* When was the domain registered?
* What is the owner’s contact information?
* Who is the owner of the IP address block?
* Where is the host situated?
2.Net Tools v4.5.74
It’s a Swiss Army Knife for everyone interested in a set of powerful network tools for everyday use.
Net Tools is cutting-edge security and network monitoring software for the Internet and Local Area Networks, providing clients with the ability and confidence to meet the challenges of tomorrow's technology. Keeping pace with the industry trends, we offer professional tools that support the latest standards, protocols, software, and hardware for both wired and wireless networks. The main goal is the creation of high quality software.
Net Tools is a very strong combination of network scanning, security, file, system, and administrator tools useful in diagnosing networks and monitoring your PC and computer's network connections for system administrators. Next to the essential core tools it includes a lot of extra valuable features.
This all-in-one toolkit includes also a lot of handy file and system utilities next to the huge amount of network tools. The menus are fully configurable, so in this way you won’t get lost in the extremely large amount of essential tools. All the additional features will make this application a must have for all system administrators. There are numerous constructive and valuable applications included in Net Tools that can be used for a great amount of purposes.
The latest version of Net Tools is hybrid; it means that it’s capable of working together with applications that are made and designed for Net Tools, so in this way more flexibility and user-friendliness is obtained.
It’s entirely compatible and has thoroughly been tested on Windows XP. With the 150+ tools it is a great collection of useful tools for network users. The size of Net Tools 4.5.74 is approximately 25 Mb.
This software is designed for the !! MS Software is not allowed !! Windows OS (Windows 98, NT, 2000, 2003, XP, Vista).
It’s a Swiss Army knife for everyone interested in a set of powerful network tools for everyday use.
Net Tools 4.5.74 contains a whole variety of network tools
Quote:
|
1) IP Address Scanner 2) IP Calculator 3) IP Converter 4) Port Listener 5) Port Scanner 6) Ping 7) NetStat (2 ways) 8) Trace Route (2 ways) 9) TCP/IP Configuration 10) Online - Offline Checker 11) Resolve Host & IP 12) Time Sync 13) Whois & MX Lookup 14) Connect0r 15) Connection Analysator and protector 16) Net Sender 17) E-mail seeker 18) Net Pager 19) Active and Passive port scanner 20) Spoofer 21) Hack Trapper 22) HTTP flooder (DoS) 23) Mass Website Visiter 24) Advanced Port Scanner 25) Trojan Hunter (Multi IP) 26) Port Connecter Tool 27) Advanced Spoofer 28) Advanced Anonymous E-mailer 29) Simple Anonymous E-mailer 30) Anonymous E-mailer with Attachment Support 31) Mass E-mailer 32) E-mail Bomber 33) E-mail Spoofer 34) Simple Port Scanner (fast) 35) Advanced Netstat Monitoring 36) X Pinger 37) Web Page Scanner 38) Fast Port Scanner 39) Deep Port Scanner 40) Fastest Host Scanner (UDP) 41) Get Header 42) Open Port Scanner 43) Multi Port Scanner 44) HTTP scanner (Open port 80 subnet scanner) 45) Multi Ping for Cisco Routers 46) TCP Packet Sniffer 47) UDP flooder 48) Resolve and Ping 49) Multi IP ping 50) File Dependency Sniffer 51) EXE-joiner (bind 2 files) 52) Encrypter 53) Advanced Encryption 54) File Difference Engine 55) File Comparasion 56) Mass File Renamer 57) Add Bytes to EXE 58) Variable Encryption 59) Simple File Encryption 60) ASCII to Binary (and Binary to ASCII) 61) Enigma 62) Password Unmasker 63) Credit Card Number Validate and Generate 64) Create Local HTTP Server 65) eXtreme UDP Flooder 66) Web Server Scanner 67) Force Reboot 68) Webpage Info Seeker 69) Bouncer 70) Advanced Packet Sniffer 71) IRC server creater 72) Connection Tester 73) Fake Mail Sender 74) Bandwidth Monitor 75) Remote Desktop Protocol Scanner 76) MX Query 77) Messenger Packet Sniffer 78) API Spy 79) DHCP Restart 80) File Merger 81) E-mail Extractor (crawler / harvester bot) 82) Open FTP Scanner 83) Advanced System Locker 84) Advanced System Information 85) CPU Monitor 86) Windows Startup Manager 87) Process Checker 88) IP String Collecter 89) Mass Auto-Emailer (Database mailer; Spammer) 90) Central Server (Base Server; Echo Server; Time Server; Telnet Server; HTTP Server; FTP Server) 91) Fishing Port Scanner (with named ports) 92) Mouse Record / Play Automation (Macro Tool) 93) Internet / LAN Messenger Chat (Server + Client) 94) Timer Shutdown/Restart/Log Off/Hibernate/Suspend/ Control 95) Hash MD5 Checker 96) Port Connect - Listen tool 97) Internet MAC Address Scanner (Multiple IP) 98) Connection Manager / Monitor 99) Direct Peer Connecter (Send/Receive files + chat) 100) Force Application Termination (against Viruses and Spyware) 101) Easy and Fast Screenshot Maker (also Web Hex Color Picker) 102) COM Detect and Test 103) Create Virtual Drives 104) URL Encoder 105) WEP/WPA Key Generator 106) Sniffer.NET 107) File Shredder 108) Local Access Enumerater 109) Steganographer (Art of hiding secret data in pictures) 110) Subnet Calculater 111) Domain to IP (DNS) 112) Get SNMP Variables 113) Internet Explorer Password Revealer 114) Advanced Multi Port Scanner 115) Port Identification List (+port scanner) 116) Get Quick Net Info 117) Get Remote MAC Address 118) Share Add 119) Net Wanderer 120) WhoIs Console 121) Cookies Analyser 122) Hide Secret Data In Files 123) Packet Generator 124) Secure File Splitting 125) My File Protection (Password Protect Files, File Injections) 126) Dynamic Switch Port Mapper 127) Internet Logger (Log URL) 128) Get Whois Servers 129) File Split&Merge 130) Hide Drive 131) Extract E-mails from Documents 132) Net Tools Mini (Client/Server, Scan, ICMP, Net Statistics, Interactive, Raw Packets, DNS, Whois, ARP, Computer's IP, Wake On LAN) 133) Hook Spy 134) Software Uninstaller 135) Tweak & Clean XP 136) Steganographic Random Byte Encryption 137) NetTools Notepad (encrypt your sensitive data) 138) File Encrypter/Decrypter 139) Quick Proxy Server 140) Connection Redirector (HTTP, IRC, ... All protocols supported) 141) Local E-mail Extractor 142) Recursive E-mail Extractor 143) Outlook Express E-mail Extractor 144) Telnet Client 145) Fast Ip Catcher 146) Monitor Host IP 147) FreeMAC (MAC Address Editor) 148) QuickFTP Server (+user accounts support) 149) NetTools Macro Recorder/Player (Keybord and Mouse Hook) 150) Network Protocol Analyzer 151) Steganographic Tools (Picture, Sounds, ZIP Compression and Misc Methods) 152) WebMirror (Website Ripper) 153) Extra Tools (nmap console & win32 version) |
the Swiss-knife for wordlists
Wordlists are used in brute force security software like GoldenEye. They contain username-password combinations (AKA."combos") which are used by the cracking tool to attack a protected web-site.
To create, enrich and maintain such wordlists you need a tool like Raptor that offers top-features to make your wordlist unbeatable. Different protection schemes require different wordlists - a wordlist that works with one site fails on another one because its username-password combos don't match the characteristics of the site protection. You don't need to create a wordlist for each protection scheme - just use your existing wordlist and manipulate it using Raptor's advanced and easy to use features.
Raptor is known to security experts for its outstanding features for years. Raptor 3 benefits of the experience gained since 1998 when the first version was released and was rapidly appreciated by a growing community of security experts. In Raptor 3, these outstanding features could be even improved.
Features
* common text processing features
* working with multiple files
* option to manipulate file on disk rather than loading them in the editor
* advanced list sorting: sorting alphabetically, by word length, by username or password
* randomizing lists to obfuscate server log files
* anagrams
* splitting combo files in single lists and vice versa
* fast duplicate remover allows to use reference lists and to save duplicates
* powerful and customizable filters to remove unwanted words or combos
* customizable wordlist manipulations to enrich and enlarge your wordlists
* wordlist and URL converters
* list generators for various AVS formats and a powerful and flexible ALS list generator
* online and file password leecher
* support for Windows™ XP visual styles
* and many more
4.Net Detective
With Net Detective Online you can...
» Screen prospective employees - before you hire them.
» Check their credit, driving or criminal records Verify income or educational accomplishments.
» Track down people who owe you money and find hidden assets.
» Locate an old friend, a missing relative, even a lost love.
» Find e-mail, telephone or address information on most anyone!
» Investigate your family history - trace your family tree.
» Check birth, death, adoption, or social security records.
» Check military records for Army, Navy, Air Force or Marines.
» Check out your daughter's new boyfriend.
» Find trial transcripts and court orders.
» Find out how much alimony someone is paying.
» Find employment opportunities "All Over The World" AND SO MUCH MORE THE LIST GOES ON AND ON...
5.Cain & Abel
It is a password recovery tool for microsoft windows Operating Systems. It allows easy recovery of various kind of passwords by sniffing the network, cracking encrypted passwords using Dictionary, Brute-Force and Cryptanalysis attacks, recording VoIP conversations, decoding scrambled passwords, revealing password boxes, uncovering cached passwords and analyzing routing protocols.
The program does not exploit any software vulnerabilities or bugs that could not be fixed with little effort. It covers some security aspects/weakness present in protocol's standards, authentication methods and caching mechanisms; its main purpose is the simplified recovery of passwords and credentials from various sources, however it also ships some "non standard" utilities for !! MS Software is not allowed !! Windows users.
Cain & Abel has been developed in the hope that it will be useful for network administrators, teachers, security consultants/professionals, forensic staff, security software vendors, professional penetration tester and everyone else that plans to use it for ethical reasons. The author will not help or support any illegal activity done with this program. Be warned that there is the possibility that you will cause damages and/or loss of data using this software and that in no events shall the author be liable for such damages or loss of data.
6.XL Delete 1.3
XL Delete is a powerful secure delete tool that will permanently delete any of
your files using one of its twelve wipe methods or with a custom method that you
create. Many people believe that emptying the recycle bin will delete a file forever.
This is not true, when you delete a file and empty it from the recycle bin, the file is
in fact still on your hard drive. The only thing that happens when you empty the recycle
bin is that Windows marks the area where the file is on the hard drive as overwriteable
so that it can reuse the space when necessary. This allows special data recovery software
to be able to actually undelete the file and view all of its original contents.
Features at a glance:
• 12 Different wipe methods to choose from including Peter Gutmann's method.
• Define your own custom wipe methods.
• Easy to use wizard mode. Delete any file or folder in 3 simple steps.
• Shell integration, including integration with the Recycle Bin.
• Ability to wipe all the free space of any selected hard drive.
• Ability to securely lock the free space of any selected hard drive.
• Integrated scheduler that allows you to schedule the secure wiping of files and folders.
• Works on memory cards, usb drives, and other types of removeable media.
• Drag and drop support for files and folders.
• Cryptographically secure random number generator for maximum protection.
• NEW: Ability to force wipe files that are in use.
• NEW: Enhanced help tool tips.
7.Triton II
It's the next logical step.
This program is what is known as an "exploiter". It can be used to probe websites for possible vulnerabilities based on user-customisable pre-defined lists. This is a follow up to the popular -=[Triton 0.3]=- program with a great number of improvements.
This program should only be used against sites where you have the permission to do so.
8.IPnetinfo
Description
IPNetInfo is a small utility that allows you to easily find all available information about an IP address: The owner of the IP address, the country/state name, IP addresses range, contact information (address, phone, fax, and email), and more.
This utility can be very useful for finding the origin of unsolicited mail. You can simply copy the message headers from your email software and paste them into IPNetInfo utility. IPNetInfo automatically extracts all IP addresses from the message headers, and displays the information about these IP addresses.
And much more....
[No leeching please]
Code:
http://rapidshare.com/files/42788328/Tools.rar



 3:19 AM
3:19 AM
 salligaramu
salligaramu

 Posted in:
Posted in: 




0 comments:
Post a Comment